When Revoking a Token Wipes a Machine: How We Responded to Mini Shai-Hulud
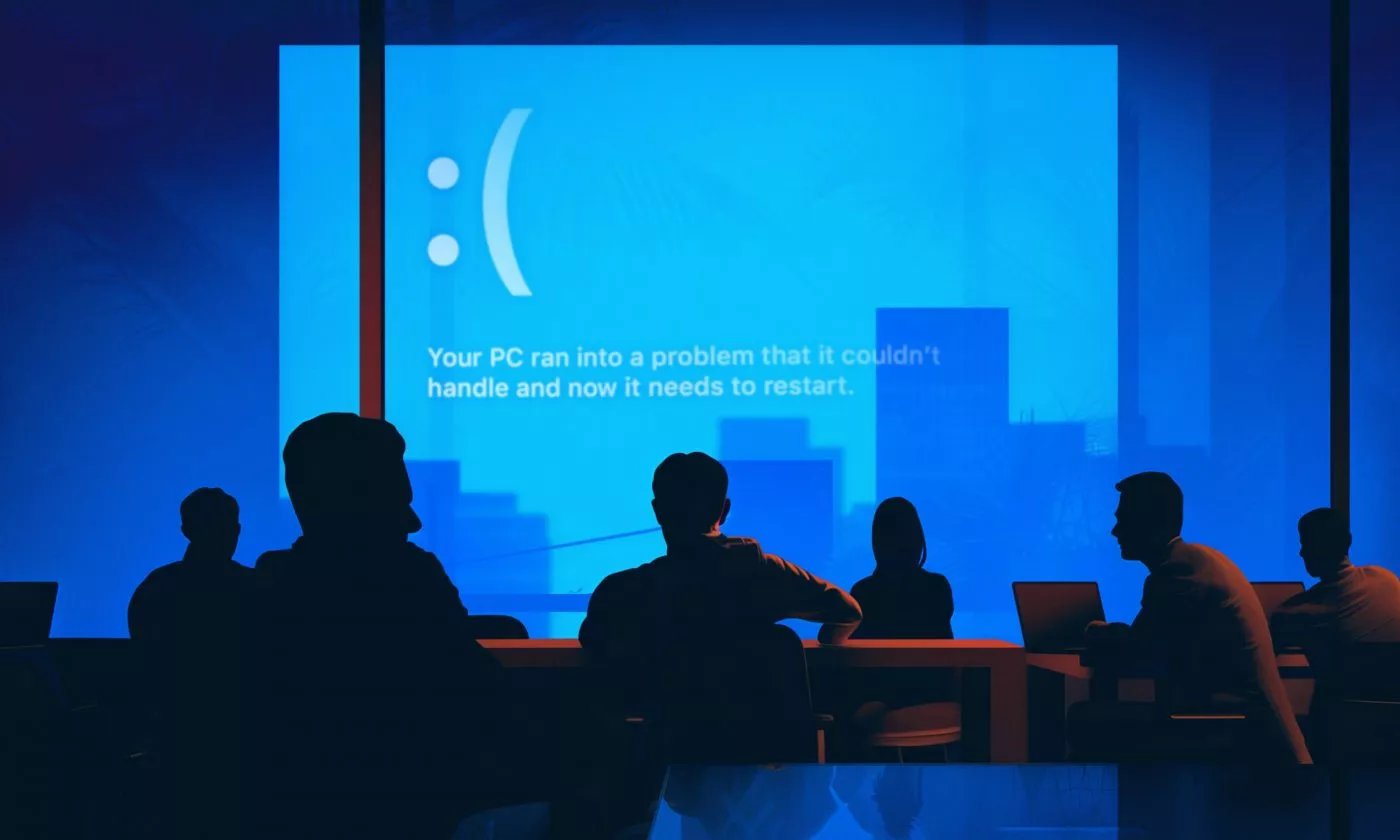
Mini Shai-Hulud turned credential revocation into a machine-wiping trap. Here's what our incident response looked like, and what your team should change before the next one.
,