Pen Testing, Red Teaming, and Why No Scanner Can Replace Either
Pen testing and red teaming are often used interchangeably. They're not. Here's what each actually does, when you need which, and why automated scanners can't replace either.

Pen testing and red teaming are often used interchangeably. They're not. Here's what each actually does, when you need which, and why automated scanners can't replace either.
axios is the JavaScript library most apps use to talk to the internet. On March 31, two malicious versions were quietly published to npm — and anyone who ran npm install during a three-hour window may have a remote access trojan on their machine. Full technical breakdown inside.
Discover how hackers bypass Android root detection, anti-hooking, and anti-debug protections with real code examples and penetration testing techniques to strengthen your mobile security knowledge.
We asked AI to build three web apps with different levels of security guidance, then tried to break them. Here’s what we found.
An evaluation of AI-generated code security found that while detailed security prompts lead to improved outcomes, consistent vulnerabilities and gaps remain even with strict guidance.
Learn how MOD suppliers can prepare for CSMv4 with support from a DCC Level 1 certified company.

OpenClaw showcases how powerful “local-first” AI agents can be, but it also shows how quickly convenience can turn into a security liability.

The clock’s ticking: the Cyber Resilience Act brings strict security rules across your product’s lifecycle.

Cybersecurity in 2026 is all about AI-driven attacks, stricter global regulations, and supply chain exposure – here's how to stay ahead.
Software supply chain security is now critical to protecting not just your code, but everything your code depends on. Learn how to secure your systems.
Discover how cybercrime grew into a $10.5 trillion economy in 2025 and why resilience, not luck, is the only defense.

Discover the latest cybersecurity trends for 2025. Arm yourself with the knowledge and tools to stay secure in the face of evolving threats.
Discover how adopting the Secure Development Life Cycle (SSDLC) can strengthen your application's security against ever-evolving cyber threats.
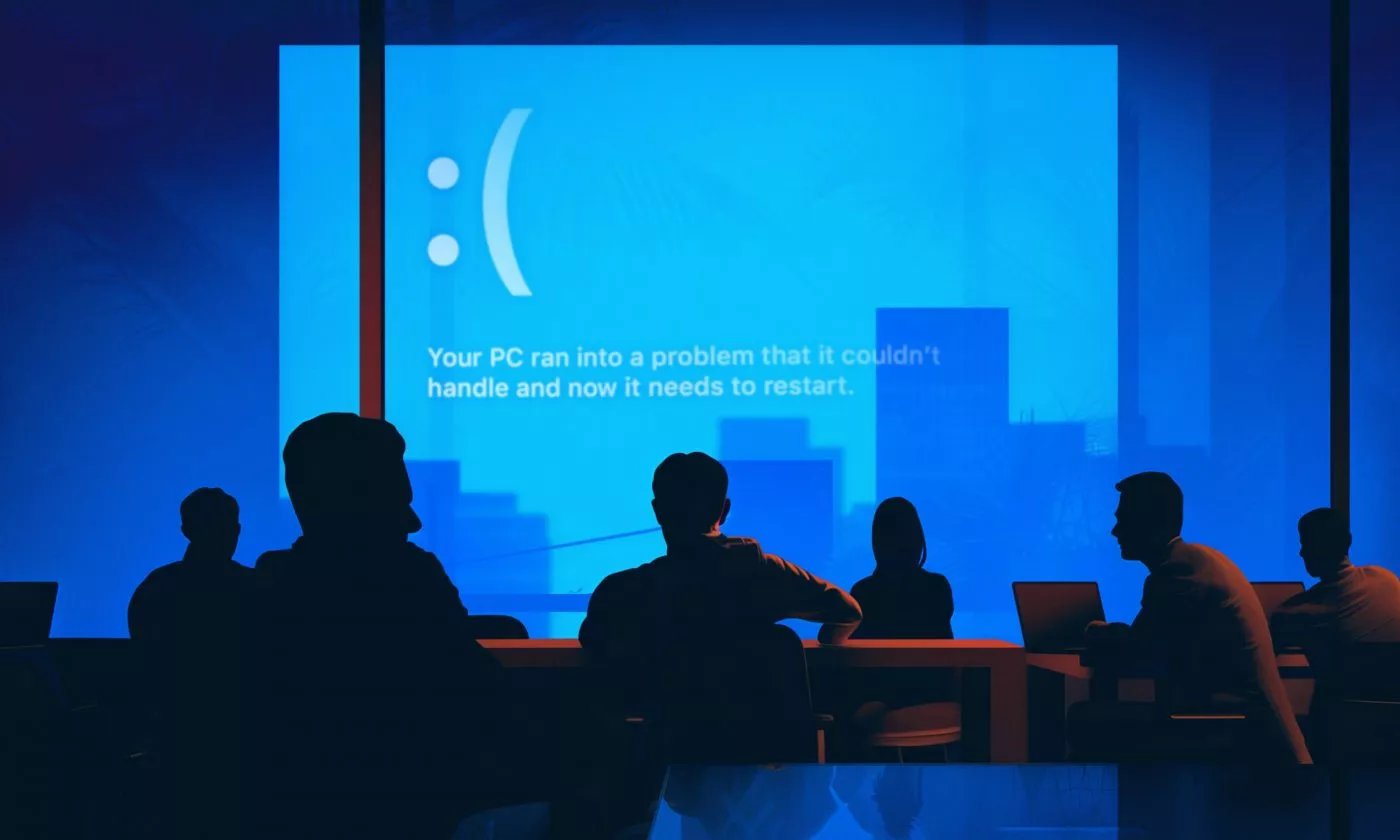
Infinum's SecOps team director shares what we can learn from the incident that got 8,5 million screens worldwide singing the blues.

We demystify NIS2 and DORA, the two powerful pieces of cybersecurity legislation in the EU, and explain what they mean for your business.

Find out and strengthen your defenses by identifying weaknesses and educating your teams.

We take you through all the penetration testing steps, explaining how each of them helps identify weaknesses in your security system.

As a supermassive data breach brings security in the spotlight, we identify the cybersecurity trends that will help you navigate 2024's digital landscape.

The main reason why penetration testing is important is that it allows us to view your product with a hacker’s eyes.